UIDAI: A devil in the works
By now, many in the general public would already be aware that the UIDAI has been making the headlines in various newspapers for the wrong reasons, but is Aadhar in the right in its main mission, and is it worth it to stick around for the fruits of this system? In order to analyze and critique the main features of the system, we will start from the beginning where the UIDAI committee rolled out its vision and defined the program with the following main theme:
The UIDAI is a non-mandatory 12-digit individual identification number, which will be highly centralised, pro-poor. It will not be a citizenship card and will not be open to NRIs. This number will serve as a proof of identity and address, anywhere in India. Each individual needs to enrol only once which is free of cost. Aadhaar number will help provide access to services like banking, mobile phone connections and other Government and Non-Government services in due course. The UIDAI information will not be accessible to public and private agencies. [1]
This introduction should cause people to be deeply suspicious of the motives of the government. In this little essay, we will prove that promises of this system being non-mandatory and its data being secure have already proven to be untrue. And whatever else that remains in the rest of the paragraph or is intended by the UIDAI designers is very, very dangerous for society in general.
Readers must realize that when a computer system (or any other service/ product for that matter) does not deliver what it promises, say a tag reader system in a shopping centre does not work, the system is either transformed into a much better one by the owner and it delivers the goods at a mutually agreeable cost, or the company or that particular division within a company completely stops manufacturing the system, books its losses and shuts shop. But that’s in the private sector. What we are dealing with here is a public system with public funds, public ownership, but a completely hidden and obfuscating system of responsibility that shape-shifts and plays the chameleon with the blessings of the government. The costs of this system are also hidden from plain sight and funds are drawn from the government and people are told that enrolment is “free of cost”. This gives the wrong impression to citizens, as exactly the opposite is true – this system has so far cumulatively cost us over Rs2,920 crore. [2] Quoting Gopal Krishna, Member, Citizen’s Forum for Civil Liberties: “It is reported that the UIDAI estimates the project will costs Rs. 45,000 crores to the exchequer in the next 4 years. This does not seem to include the costs that will be incurred by Registrars, Enrollers, internal systems costs that the PDS system will have to budget if it is to be able to use the UID, the estimated cost to the end user and to the number holder.” [3] If we allow this system to come into force, it will not go out of business. Instead it will receive bigger funds and losses will never be an issue. Just look at the examples of MTNL [4], BSNL [5], Air India [6] and Scooters India [7].
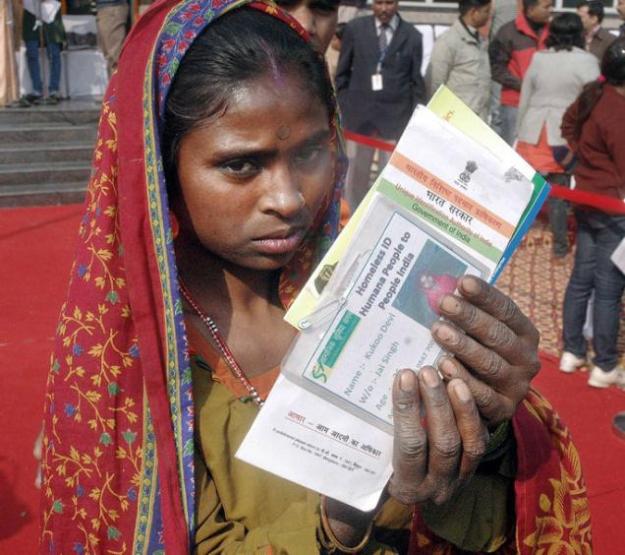
An RTI enquiry by Mr Goyal reveals that the UIDAI concept was first imagined by the Planning Commission to deliver, primarily, welfare services. This was not formalized for reasons relating to “security”. The administration of welfare is being done under the guise of “identification”. Its clear implication is that if you are poor and you do not have a unique identification number, then you don’t exist, and you cannot access government services and non-government services, in due course.
What about that little clause at the end of “non-government services”? Today, there are so many government “services” that we choose to access or are forced to access: trains, buses, children’s education and hospitals. Maybe if you apply for an RTI, you have to quote your UIDAI number, just like a serial identification number on your laptop. But tomorrow, who knows what non-government services will be brought under ambit? The possibilities are frightening. As an opening shot [8], the government announced the launch of Saral Money to open bank accounts by tying five banks (SBI, HDFC Bank, ICICI Bank, Indian Overseas Bank and Axis Bank) through a Visa payment gateway, using the Aadhar unique ID number as a proxy for cumbersome Know Your Customer (KYC) norms. The key to the new solution is Visa network, which integrates and links the different systems being operated by banks with the government’s national identity database.
This is the sort of public-private partnership that privacy advocates should dread – indeed, Julian Assange, the head of WikiLeaks, had famously branded the likes of Visa, MasterCard, PayPal and others as “instruments of US foreign policy” in Dec 2010 after a number of companies hosting WikiLeaks’ online operations, including Amazon and PayPal, terminated their relationship with the whistleblowers’ site after pressure from Joe Lieberman, chairman of the US homeland security committee.
And who controls the UIDAI? It’s not even clear [9]. Just as in the recent massive hoax of the commonwealth games in New Delhi, typical obfuscation is apparent as lines of responsibility are not clear inside a complex web of government departments.
Examining some basic specifications of the Aadhar machinery
The UIDAI number will not be used just for verification (Are you who you claim to be?), but as is repeatedly stated on the official website, for identification (Who are you?). Any computerized system which delivers such services, must exclude certain data points in some cases to make the system watertight in identifying/ verifying. As such, the Aadhar system will have to refuse to perform its basic function – to identify human beings – no matter what the exceptional circumstances are, however limited the number of cases there may be, and whatever be the limited time-frame. That a human being can be de-identified in this way is by itself a despicable and unacceptable idea. This basic realization itself should completely nullify and invalidate the UIDAI’s main objective to identify, because in saying that it wants to include you in identification, it may end up excluding you from basic identification.
As far as security of data goes, this responsibility of being a good boy is with the state (access will be restricted some remote department in Delhi, and it is not even clear which department, as discussed above) and its biometric data collecting machinery (which will be, at least partly, privatized. Even if it isn’t privatized, good luck if you think that this kind of data is safe in the hands of the government! Reports are that some of the data has already been leaked/ lost as is discussed below). Furthermore, the UIDAI number will be used for tracking purposes. Ram Sewak Sharma, the Director General and Mission Director of UIDAI, said [10] that the Aadhar ID number will have four digits (termed as ”virtual number”) hidden from the individual, which will change as and when the resident changes his pin number or residence. It may be that grouping numbers of people from the same geographical area will help the efficiency of the database, but that is not what we were told the system was for. The official purpose of the Aadhar is to help identify, not to help locate. For generations we have been used to long queues that extend for 15-20 minutes if not for hours together. Clearly, there would be little to lose if one had to wait for a couple of seconds more, if speedier databases is the excuse for this mischief.
There is a large conditional clause on the voluntary nature of the Aadhar number. The Central Government has sent out a directive that unless a district has 80% registration, providing subsidies through Aadhaar cannot be undertaken [11]. Some of these people would have been entitled to receive the welfare earlier. To clarify, I am not in favour of subsidies in the first place. Subsidies and social welfare are bad economics that keep under-performing businesses and inefficient systems alive and drain the wealth of hardworking people in efficient systems through taxations of all forms. If the government’s end motive is to not pay subsidies, then there would be no need for this massive government machinery of welfare departments and identification numbers, and our taxation burdens would be reduced tremendously. Then we could actually keep what we earn and invest in opportunities we deem credible. But even if subsidies have to be given through bank accounts, why not let the individual banks handle it? They can expand (depends on whether it is cost efficient for them to invest in bank branches in certain areas), make their systems more efficient (depends on whether they choose to invest in mutually understandable protocols/ systems) and do away with this all encompassing supreme one-nation centralized identity mechanism. Thus, what is actually transpiring is that the government wants to make people dependent on its system, arm-twisting us into ceding our civil liberties all in the name of welfare, which is a failed concept in the first place; ultimately the government wants to control our very existence and identity, leaving no stone unturned to entice people into the system, sometimes even forcing them into it.
On data security, just by pure logical deduction, one should be very concerned of such a mass-centralized database offering private citizen’s data. We would be relying on the “right man on the horse” to not misuse this centralized personal information such as telephone number, address, passport, driving license number, finger prints and iris scans. But let’s get into the details and find out what else lies in store for us.
Mr Nilekani’s plans to part-privatize the data owning companies [12] offer bleak prospects for security and sanctity of private data of the citizens [Another clarification that far from being anti-privatization, I am actually pro-privatization. But not in this crony-capitalistic way where the state draws money from public coffers without consent and private companies are allowed to then make a buck out of such an enterprise, for no risk, and to continue to receive, albeit, a finite reward. A true capitalistic, voluntary, private institution of UIDAI can be imagined, but it is likely to remain just that – an imagination – because clients of such a company may fear public rebuke at the idea of data-trading and there may be very few people who would want to give data voluntarily to such data-owning companies in the first place]. And in any case, that the guarantee of data security given to us by the government has failed has already been proven – data gathered has already been bungled in multiple cases. [13]
Another point to discuss: “pro-poor”. In fact, what they are really doing is threatening those who are not currently categorized as “poor” to take the UIDAI number, else they will not give the poor the subsidies for which money has already been paid for through taxation by the citizenry and allocated for in the planned/ non-planned expenditures of the government. And they will not only not give subsidies to the poor, but also bar them from using public services such as schools. In some schools, even the non-poor are being forced to enrol in the UIDAI program. [14] All in all, this is massive program not to give “identity” but to threaten “de-identification” and thus to exclude Indians from any and all kinds of government and non-government services – a true Orwellian concept.
Moreover, the UIDAI doesn’t even serve the purpose of convenience for the individual; the official website clearly states that the UIDAI number will not replace other IDs. So it doesn’t reduce the individual’s paper carrying burden either.
Yet another point to discuss: Why the iris scans? The iris scans are not necessary if finger prints and names and addresses are already present in the data bank for verification of identity. Moreover, iris scans have been proven to be duplicable, which raises doubts over the very purpose of their inclusion in the list of biometric data sought by the UIDAI. In an article on “Electronic Frontier Foundation” dated 27th July 2012 [15], Javier Galbally, an Assistant Researcher at Universidad Autonoma de Madrid and recipient of a number of distinctions, including IBM Best Student Paper Award at ICPR 2008, and finalist of the EBF European Biometric Research Award, revealed that it is possible to spoof a biometric iris scanning system using synthetic images derived from real irises. A Wired article hit on the significance of this discovery: “This is the first time anyone has essentially reverse-engineered iris codes to create iris images that closely match the eye images of real subjects, creating the possibility of stealing someone’s identity through their iris.” [16]
In the news recently [17] was also how the PSU banks themselves, such as SBI, are unhappy with UIDAI over a) fiduciary responsibility of contingent losses due to “false identification” if UIDAI numbers are used in cash transfers and b) the implementation of a specific computer system (UIDAI-NPCI) for cash transfers as prescribed by the UIDAI. Not only that, the article reveals that subsidies are being doled out and some banks are being pressured into accepting the UIDAI-NPCI system.
In brief, the UIDAI system is already a broken one. So, it should also be no great shock for readers to learn that a Parliamentary panel headed by former Finance Minister Yashwant Sinha had stated on 22 Apr 2013 that it was concerned that in the last three financial years a huge sum of Rs. 2,300 crore had been spent on UIDAI despite lack of legislative sanction of the scheme. [18] “In the absence of legislation, Unique Identification Authority of India (UIDAI) is discharging its functions without any legal basis,” the committee had said. The same panel had rejected a draft UIDAI bill about 17 months ago.
Dark linkages of UIDAI with the National Population Register (NPR)
The linkages with NPR are meant to be UIDAI’s excuse for making registration compulsory and the data non-confidential.
A person who has already enrolled with some other Registrar of UIDAl still has to register under NPR. [19] Under the NPR, certain processes such as the collection of data at the doorstep of the individual by authorized persons, collection of biometrics after following a certain process, authentication through social audit, verification by authorities, etc. are mandatory. Thus, a person who has already enrolled with some other Registrar of UIDAI will have to register under NPR again. The same page goes on to state the following connection between the NPR and UIDAI: The data collected in NPR after authentication will be sent to UIDAI for de-duplication and issue of Aadhaar Number. Thus the register will contain three elements of data – (i) demographic data, (ii) biometric data and (iii) the Aadhaar (UlD Number). Thus the conclusion can be drawn that a human being residing in India mandatorily has to register oneself under the NPR, provide data such as one’s educational qualifications, occupation, not to mention one’s iris and fingerprint scans, all of which is non-confidential data. [20] The UIDAI can be likened to being just a department of the government which “de-duplicates” information already covered by the NPR and doles out an identity card, known as the Multi-purpose National Identity Card (MNIC).
Quoting Mr R Ramakumar, Tata Institute of Social Sciences, Mumbai: “There is no mention of the collection of biometrics of individuals in Citizenship Rules 2003, which empowers the NPR. The collection of biometrics was stealthily made part of the NPR sometime after 2003. This stealth measure allowed the UIDAI to piggyback on NPR, thus allowing for quick enrolment.” [21] He goes on to state that the UIDAI plunged into iris data collection even as no cost-benefit analysis was done for the overall project. “Will anyone in the government stand up and be accountable for these spending decisions?”
Moreover, in the recently concluded census in 2011, caste enumeration was conducted in conjunction with the NPR and biometric data collection. In a letter to the Group of Ministers on caste Census, the Hindu voiced its concerns by saying: “The collection of caste data at the stage of biometric capture would be cumbersome and time consuming. Outside agencies are likely to be involved, and therefore there are chances of data gathering being compromised because it would be tagged on to the huge task of biometric documentation of about 84 crore Indians… The Census Act 1948 provides strong protection for all data collected by the Census, and this has ensured that the Census — which necessarily collects individual information — has released only aggregated and anonymised data. Given the absence of such protection under the Citizenship Rules of 2003 — which governs the NPR and the biometric data capture process — there is every chance of the confidentiality of caste data being breached.” [22]
Parallel systems of government surveillance: people fighting back to restrain dictatorial governments who are getting out of hand
The collection of caste-related data during the census has a somewhat severe international historical precedent. Eerily, what the Indian government authorized in 2011, a certain Adolf Hitler government authorized in Nazi Germany with the help of IBM’s inventions of the Hollerith punch cards and racial census, “not just to count the Jews – but to identify them”.
In his award-winning book “IBM and the Holocaust”, author Edwin Black exposed how IBM and its subsidiaries helped create technologies step-by-step from the identification and cataloguing programs of the 1930s to the selections of the 1940s in order to enable the Third Reich in its plan of conquest and genocide. IBM technology was used to organize the identification of the Jews in censuses, registrations, ancestral tracing programs, running of railroads and organizing of concentration camp slave labour.
Consider a report published by UK’s Guardian which said in March 2013 that the United State’s NSA gathered some 6.3 billion pieces of computer network data in India. [23] Meanwhile, the Indian government has itself introduced a Central Monitoring Service, an intelligence agency capable of recording and monitoring internet data and telephone conversations. [24]
In the case of United States, the Department of Homeland Security (DHS) can already access the FBI and Defense Department fingerprint data. With the aid of the US-VISIT system, it can now tap into the database of four other countries – UK, Canada, Australia and New Zealand. This goes to prove that if a biometric database is allowed to exist, it will inevitably be an excuse for security, and will inevitably be shared with foreign forces to “make the system more efficient” or to “share data in real time to speed up criminal investigation” or other such purported reasons will be presented.
Elsewhere, the governments of UK and Philippines have outright rejected such projects. In Australia in the state of New South Wales, a major court case was won recently by an activist, banning public surveillance using CCTVs. Elsewhere, in Israel and in the US, government owned centralized public databases containing biometric information are under severe attack from common citizenry. In March 2013, the UK Home Office launched a public consultation of biometric data retention, stating that even under the guise of security, biometric data collection has to be extremely restricted and freedoms preserved necessarily. In a case in London, reported in Apr 2013 at a MedConfidential event involving a particular Human Genomics Strategy Group (HGSG), illustrates that if not stopped in its inception, any database, even a criminal one, can be expanded into a total police state under the auspices of medical/ biological testing. And there is, of course, the perennial alibi: security.
What about Mr Nilekani? What about the Planning Commission?
An IT services CEO of the most successful firm in the industry at that time in India, Mr Nandan Nilekani felt compelled to offer his services to the country’s government. As if backing such an authoritarian system was not a problem enough of itself, his call for part-privatization of the data owning companies is terribly unfortunate and misplaced in the least, and smacks of malfeasance and crony-capitalism at worst. Should he be asked to resign immediately, thus preventing the assemblage of this human-enslaving digital surveillance machinery?
But if we are head hunting, then we will be misguided if we stop there. The buck stops with his recruiter, the goverment, more specifically the Planning Commission. What were its motives in coming out with such a bold plan with such large expenditures. The flaws showed up within 5 yearsof its inception with many instances or arrogance and coercion by government institutions and officials being reported, this government department has truly gone out of control to think that it could get away with such a heinous conception. I believe that whilst there is a case for believing that Mr Nilekani was being fooled and played by the government all along (An article by Dr Usha Ramanathan, an independent law researcher, points to the fact that since Mr Nilekani was appointed the chairperson of the UIDAI, in the rank of a Cabinet minister, he has chaired multiple committees, each of which pushes for the collection of data and the creation of databases, and steers the government to become a customer of whoever controls the database), there is no case for defending the government. The government and its department were pulling the strings all along – this was no accident, this was by the deliberate design of the government & the Planning Commission. [12]
Steps to take in order to solve the problem in the best way we can
First and foremost, the individual can destroy the UIDAI card/ document that he/ she possesses. Second of all, the individuals, if in agreement with the points of view presented here, can take action at the local level and ban UIDAI officials from entering their premises, of say a house or even a housing society. But most of all, people should resent and resist this system at all and any possible opportunity and as publicly and aggressively as possible, but without any civil disruption or violence. Citizens can start blogging on the internet and voicing their opinions on mass media. If the people resist and refuse to provide data, the system will lose legitimacy and cease to exist. If we can reach out to the employees on the ground, who work for these technology companies in UIDAI projects and governmental departments, they too could be encouraged to abstain and seek exclusion from those projects. And very importantly, if we can be vociferous enough and capture the mainstream line of thought, the government will have to crawl back into its cave and red-light this system.
Notes
[1] Excerpted from the official UIDAI website.
[2] Source: official UIDAI figures for FY10-FY14 up to May 2013.
[3] “298 – 764 – On the UIDAI – EPW article” http://saynotoaadhaar.blogspot.in/
[4] The article “BSNL-MTNL merger: Does government want to repeat Air India folly?” points out that MTNL and BSNL may be merged after their network infrastructure and land assets are spun off into separate companies. Thus, we will have one infrastructure company, one land company and the third will be the merged telecom services entity. Merging the two is no recipe for revival when the problem is overstaffing and lack of managerial autonomy.
[5] Source: Pvt telcos against government aid to BSNL, MTNL for surrendering BWA spectrum. Not surprisingly, private operators feel aggrieved as the state continues to buttress the public sector operators. In a letter to communications and IT minister Kapil Sibal on January 29, private telecom operators associations – Association of Unified Telecom Service Providers of India (AUSPI) and Cellular Operators Association of India (COAI) – said that any refund or financial support provided to the PSUs against the National Telecom Policy and would be “unfair to the entire industry and it will severely distort the level playing field and competition of the industry.”
[6] Government audit blames ministry, management for Air India troubles
[7] How our tax money rides away on Scooters India
[8] As described in this Hindustan Times article in December 2012.
[9] An RTI request by Mr Goyal clearly states that the UIDAI autonomously designed the database, that the UIDAI’s location within a section of government was not clear after the first five years.
[10] Quote taken from an article in Apr 2010 in Business Standard, “16-digit Aadhaar to have four hidden numbers”.
[11] Aadhaar card: Many worried about privacy
[12] Aadhaar: Private ownership of UID data- Part I
[13] Per Postnoon in May 2013, biometric information of 14 lakh Aadhar applicants missing in Hyderabad; Per Times of India in April 2013, Maharashtra lost data of 3 lakh UID cards.
[14] Per Times of India in Apr 2013, Aadhar is being forced upon government aided schools and oil marketing companies in Mumbai.
[15] Red Flag On Biometrics: Iris Scanners Can Be Tricked
[16] Reverse-Engineered Irises Look So Real, They Fool Eye-Scanners
[17] PSU banks express reservation against usage of Aadhaar number for cash-transfers
[18] UIDAI bill for Aadhaar number anytime, anywhere
[19] As per the FAQ page of the DIT’s NPR website.
[20] R.C. Sethi, additional registrar general of India, in an article in the Wall Street Journal: “The Census is being done under the Census Act 1948 and information collected in the Census is confidential. The information collected in the NPR is not confidential.”
[21] From an article in the Hindu, in Sep 2011.
[22] Letter to the Group of Ministers on caste Census




Pingback: UIDAI’s connection to the conspiracy against modern human society | Liberty Here and Now
Pingback: UIDAI Official website revamped | Simple Financial Mantras